The Defense Department on Monday became the first U.S. government agency to launch a policy enabling researchers to report bugs or flaws they discover in its websites without fear of prosecution.
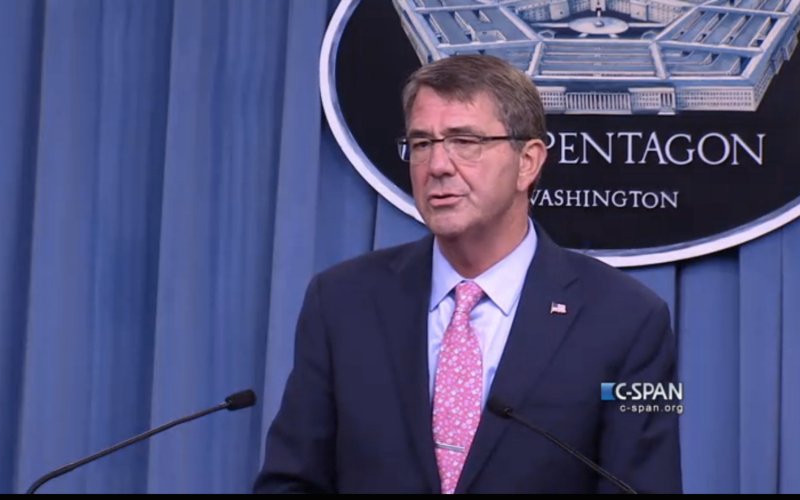
Calling it a “see something, say something” policy for the digital domain, Defense Secretary Ashton B. Carter said the program is aimed at improving the security of the Pentagon’s unclassified, public-facing networks.
The Army also opened registration Monday for Hack the Army, a challenge in which researchers and hackers scour Army sites for software flaws and compete for thousands of dollars in bounty rewards.
The Army contest explicitly authorizes researchers to try to hack a limited set of Army systems to find weaknesses. Meanwhile, the new policy is aimed at creating a way for hackers or researchers who come across flaws to report them without exposing themselves to criminal liability.
“This is a historic moment for hackers and the U.S. government,” said Katie Moussouris, founder of Luta Security and an adviser to the Pentagon on the new policy. “For the first time since hacking became a felony offense over 30 years ago, the Department of Defense has now opened the doors for ongoing vulnerability disclosure from helpful hackers who want to help secure these systems without fear of legal prosecution.”
There are security researchers who conduct broad scanning of internet systems to discover and map vulnerabilities. In doing so, they might come across flaws in Pentagon websites. There are also hackers who, for an intellectual challenge, probe systems to try to find flaws that might be exploited. In either case, these researchers and hackers could be charged with violating the Computer Fraud and Abuse Act, a prospect that has chilled security research.
Assistant Attorney General Leslie Caldwell, head of the Justice Department’s criminal division, called the new policy “a laudable way to help computer security researchers to use their skills in an effective, beneficial and lawful manner to reduce security vulnerabilities.” Her division advised in the crafting of the policy.
Pentagon networks are under constant assault from hackers seeking to find weaknesses they can exploit. In recent years, there have been intrusions into the unclassified email systems of the secretary of defense and at the Joint Chiefs of Staff. In 2008, the department’s classified network was compromised in an operation thought to have originated in Russia.
The vulnerability disclosure policy will provide a standard avenue of reporting for all department websites. Bug data that is reported will be used for defensive purposes only, the policy states, to fix vulnerabilities in the department networks or applications, or in the software of vendors.
Individuals who report flaws will not receive bounties. The policy states that they may not harm the network, withdraw any data, compromise the privacy of department personnel or disclose details of the vulnerability without permission from the Pentagon.
The policy is aimed at people who come across the bugs in the course of their jobs or through research, said Alex Rice, chief technology officer and co-founder of HackerOne, a tech firm that helps companies set up bug-bounty and vulnerability disclosure programs. It has been working with the Pentagon on the program.
“The Department of Defense is not explicitly asking them to hunt for vulnerabilities,” he said, “but they want to make sure they have a clear line of disclosure when they find them.”
The program grew out of Hack the Pentagon, a bug-bounty challenge earlier this year in which about 250 people found and submitted flaws found in Pentagon sites. Of those, 138 received bounties totaling $75,000. One of the lessons learned from that experience, Rice said, was the lack of a way for people to report these vulnerabilities to the department outside of the bounty program.
The new policy does not cover the use of bugs for offensive or hacking purposes. The White House has a separate policy addressing that issue as applied to government agencies that discover or purchase software flaws. Tech policy experts have called for more disclosure of the policy’s details and how it has been implemented.
(c) 2016, The Washington Post · Ellen Nakashima
{Matzav.com}











Yeh right. What about bugs in our cholent beans? Strawberries? Lettuce? Will the DOJ get rid of such dangerous bugs?